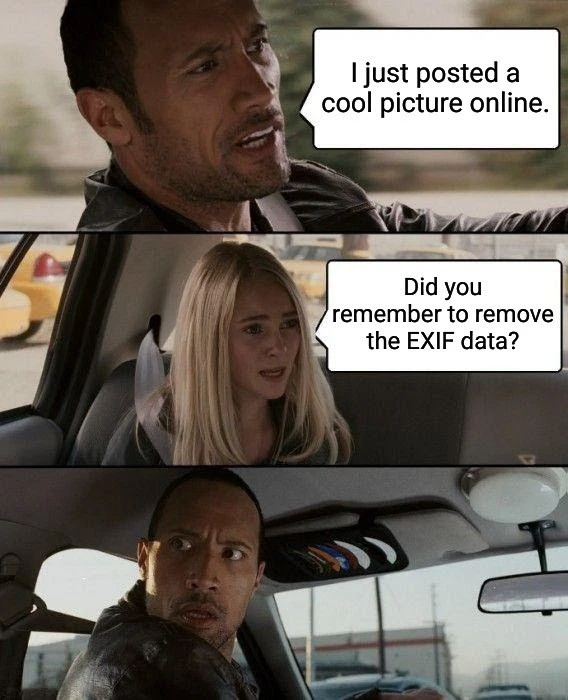
As a painfully oblivious layman, what is an exif data and how do I remove it?
Operations Security (OPSEC)
Welcome to the first operations security (OPSEC) community on Lemmy!
This is a space dedicated to discussing, sharing, and learning about operational security practices. Whether you are a business owner, a cybersecurity expert, or just a regular person, you can always benefit from a little extra OPSEC in your life.
Community Guidelines
As we belong to Lemmy.zip all of their guidelines apply on top of ours.
-
Stay on topic:
- Keep discussions related to OPSEC only
- If your post is about this community instead of OPSEC prepend [META] to the title
-
No illegal content:
- Do not discuss, promote, or engage in illegal activities
- While OPSEC can be used for criminal activity, we will not offer assistance to anyone planning to use it for such
-
Quality Content:
- Provide only good, factual and credible advice
- Avoid spreading misinformation or unverified claims
- Avoid low-effort posts, spam and sensationalism
- Copypastas are allowed only as comments and if related to the post or parent comment.
- Do not post AI-generated content; anyone can ask ChatGPT for assistance so do what you do best: be a human
- Anyone giving blatantly false advice will be permanently banned
-
No Self-Promotion:
- Refrain from excessive self-promotion or advertising
- Occasional sharing of personal projects is allowed if it benefits the community
-
Threat Models:
- Do not ask for advice without mentioning your threat model
- Do not provide advice ridiculously outside the asker's threat model
- Do not provide advice without knowing the asker's threat model (except when providing general advice to the community)
What is OPSEC?
Operations security (OPSEC) is a process that identifies critical information to determine whether friendly actions can be observed by enemy intelligence, determines if information obtained by adversaries could be interpreted to be useful to them, and then executes selected measures that eliminate or reduce adversary exploitation of friendly critical information.
In simpler terms, it is the process of finding vulnerabilities that an adversary could exploit and patching them, thereby reducing your attack surface.
OPSEC is NOT a synonym for cybersecurity. It can encompass it; however, it also revolves around physical security.
Useful resources
EXIF data is sometimes appended when you take pictures and often includes things like the coordinates it was taken at (exact location), the device it was taken on, and some additional identifiers. This is, of course, bad for privacy, especially when posting online, as someone can accurately track you just from the image.
I found this article, which seems to describe how to remove it fairly well and does not appear to be sponsored.
If you don’t care about reduced quality, you can just use a screenshot of the image.
Though I think most platforms already strip it for you (or at least the really confidential stuff like location). That's what I noticed when uploading and downloading an image and comparing the data on different platforms.
Edit: I should have read the title
Yes, I already mentioned that in the title. However, it is always bad practice to rely on a third party for your privacy. Especially a third party that profits off of your data.
Exif can also be removed via shortcuts on iOS devices
Example: https://www.icloud.com/shortcuts/2027b9d938e847029a636c6faa831a08
Number 15: Burger King foot lettuce. The last thing you'd want in your Burger King Burger is someone's foot fungus. But as it turns out, that might be what you get. A 4channer uploaded a photo anonymously to the site showcasing his feet in a plastic bin of lettuce with the statement 'This is the lettuce you eat at Burger King.' Admittedly, he had shoes on. But that's even worse. The post went live at 11:38 PM on July 16, and a mere 20 minutes later, the Burger King in question was alerted to the rogue employee. At least, I hope he's rogue. How did it happen? Well, the BK employee hadn't removed the Exif data from the uploaded photo, which suggested the culprit was somewhere in Mayfield Heights, Ohio. This was at 11:47. Three Minutes later at 11:50, Burger King branch address was posted with wishes of happy unemployment. Five minutes later, the news station was contacted by another 4channer. And three minutes later, at 11:58, a link was posted: BK's 'Tell Us About Us' online form. The foot photo, otherwise known as Exhibit A, was attached. Cleveland Scene Magazine contacted the BK in question the next day. When questioned, the breakfast shift manager said 'Oh, I know who that is. He's getting fired.' Mystery solved, by 4chan. Now we can all go back to eating our fast food in peace.
Oh, f*ck it. If you guys love the joke that much, I guess it can stay.
EDIT: This is no longer a special exception, copypastas are now allowed community-wide.
It may be a copy-pasta, but it's a perfect example of what the post is about: dude does something stupid that puts the health of people at risk, and within 15 minutes both his local news and manager know about it thanks to the EXIF data on his photo.
I mean, yeah. This copy pasta is perfectly on point.
~~Please avoid spamming/copypastas.~~
Oh come on. This is directly relevant!
Honestly, the joke flew right over my head. However, it could still use some reformatting to not take up the entire screen.
~~After a bit of thinking, I decided I would NOT reinstate this comment as it is still spam.~~
~~I will allow a shortened version, though.~~
Don't fuck with the Burger King.
I just subscribed recently and this is already an extremely helpful tip for a normie. Thank you.
What happened to McAfee exactly?