this post was submitted on 13 Sep 2023
179 points (73.1% liked)
Linux
48247 readers
733 users here now
From Wikipedia, the free encyclopedia
Linux is a family of open source Unix-like operating systems based on the Linux kernel, an operating system kernel first released on September 17, 1991 by Linus Torvalds. Linux is typically packaged in a Linux distribution (or distro for short).
Distributions include the Linux kernel and supporting system software and libraries, many of which are provided by the GNU Project. Many Linux distributions use the word "Linux" in their name, but the Free Software Foundation uses the name GNU/Linux to emphasize the importance of GNU software, causing some controversy.
Rules
- Posts must be relevant to operating systems running the Linux kernel. GNU/Linux or otherwise.
- No misinformation
- No NSFW content
- No hate speech, bigotry, etc
Related Communities
Community icon by Alpár-Etele Méder, licensed under CC BY 3.0
founded 5 years ago
MODERATORS
you are viewing a single comment's thread
view the rest of the comments
view the rest of the comments
Yeah. I know that. But that's in theory. And it's more hacking, not a virus.
If that's really true, it's surely possible to find an example of a virus that did it's thing (spread) and do a bit of damage somewhere. And not just say hypothetically it's true.
I know Linux can be hacked, because I had a webserver hacked. And i see all the logs and the hundreds of login attempts per second and automatic exploits in my logfiles. I have a good idea why most of the Linux boxes get hacked. And all I've ever seen were not updated server software resulting in rootkits. 0% is viruses in my experience. Rest is proper issues and maybe the bad guys have been quicker than you. But it's mostly targeted and rare. And nothing compared to the stuff the windows guys had to deal with during the last year and switch off things until it had been patched properly. We mainly do our updates. And every few years there is a major screwup and you type in a few commands in the terminal to hotfix something. But that's mainly it. And you can't make it about any hypothetical issue. While there are supply chain attacks for example, my mom who is using Linux to write her letters and print forms is unlikely to need to learn about that. I told her she doesn't need antivirus and viruses and trojans are more an academic thing with Linux. She doesn't need to worry. I also talked about targeted attacks and being a valuable target. But that's besides the point here. Hence my question and me wanting to stay on point.
Please just prove me wrong. I'm serious. All I could find are some harmless viruses from 2003 that didn't even spread enough to have reliable numbers. Ransomware that affected 'tens of users'. And you got the easy position. I advocate for Linux on the desktop. And it's impossible to prove something is secure. I always have to go into detail, explain viruses, architecture, package managers etc to get my point across. You got the easy position. All you need is to find one counterexample.
And arguments are always the same. I do the whole talk and then say you don't need antivirus because in real-life there are no viruses. And people ask me 'but what if tomorrow there is one'. And sure. Nobody believes me when I say I've had a quick glance into the future with my crystal ball. But what kind of argument is that? What if I'm struck by lightning on the way home tomorrow if I take the bus instead of the car? I guess I'll just die then. Many people have been under the influence of 'windows-truths' for too long and can't imagine another world. Some people didn't listen to the first part of my talk. And some just want the computer to work and a simple answer. I get all of that. But it doesn't make something true or false.
Here you go https://www.cynet.com/ransomware/linux-ransomware-attack-anatomy-examples-and-protection/ literally top of the results from googling "Linux ransomware"
Cybersecurity is all about preventative measures. It's extremely irresponsible to go "yeah, it's fine, nothing bad has happened so far!". But even then that's not quite true, since you yourself have written that your servers are being attacked all the time. And privilege escalation exploits are found all the time.
When you are advocating for putting a system in a workplace, you need to do more due diligence and preparation than what you would for a personal system. Linux can be great for security! But you don't just go "yeah it never gets viruses".
Thinking about security in this manner is how all these companies have their vital data leaked all the time.
Edit: another thing, when you hear about companies hacked and all that, how often do they run Windows, and not Linux? Often that information isn't shared, and so we don't really know. But nearly all web infrastructure runs on linux, including a majority of the cloud. I'm sure a significant part of those hacks are targeted at linux systems.
And again, let me clarify, I'm talking about workplaces, companies, not personal use. Because for personal use I do agree that Linux with the defaults for most distributions is plenty safe.
And yet another article containing 0 viruses. And only targeted attacks which we've kind of excluded because it's another topic. I'm kinda halfway willing to count something like 'QNAPCrypt'. But it's mainly the fault of a single manufacturer having bad security in place. And it's not really Linux at fault. Also something like QNAP will most likely affect consumers and small companies. I'm not sure... I'd like to see some actual numbers about how that played out.
I know about security. The main question is always: "What are you trying to protect against?", "What's YOUR attack scenario." And that'll vary a great amount. It's different for companies and consumers. It's different for servers and desktop computers. It's even different for parts of infrastructure of the same company. I know about that. And I happily admit there are other kinds of attacks on Linux infrastructure. Only thing is, they're kinda rare and viruses aren't involved.
Regarding how often companies that get attacked also run Linux: That's true. But you gotta look at the case individually. If Microsoft loses an authentication key that allows access to their cloud and AWS (or something like that). Sure. It's potentially a severe attack on their infrastructure. They have been compromised. And they also run Linux servers. But how does that relate to the existence of Linux viruses?
Yes, they're targeted attacks. That's the point. That's what you will be facing when putting Linux in your workplace. The main threat for workplaces will be targeted attacks.
So saying that putting Linux in your workplace because it has no viruses is irresponsible. Or at the very least it's lying by omission.
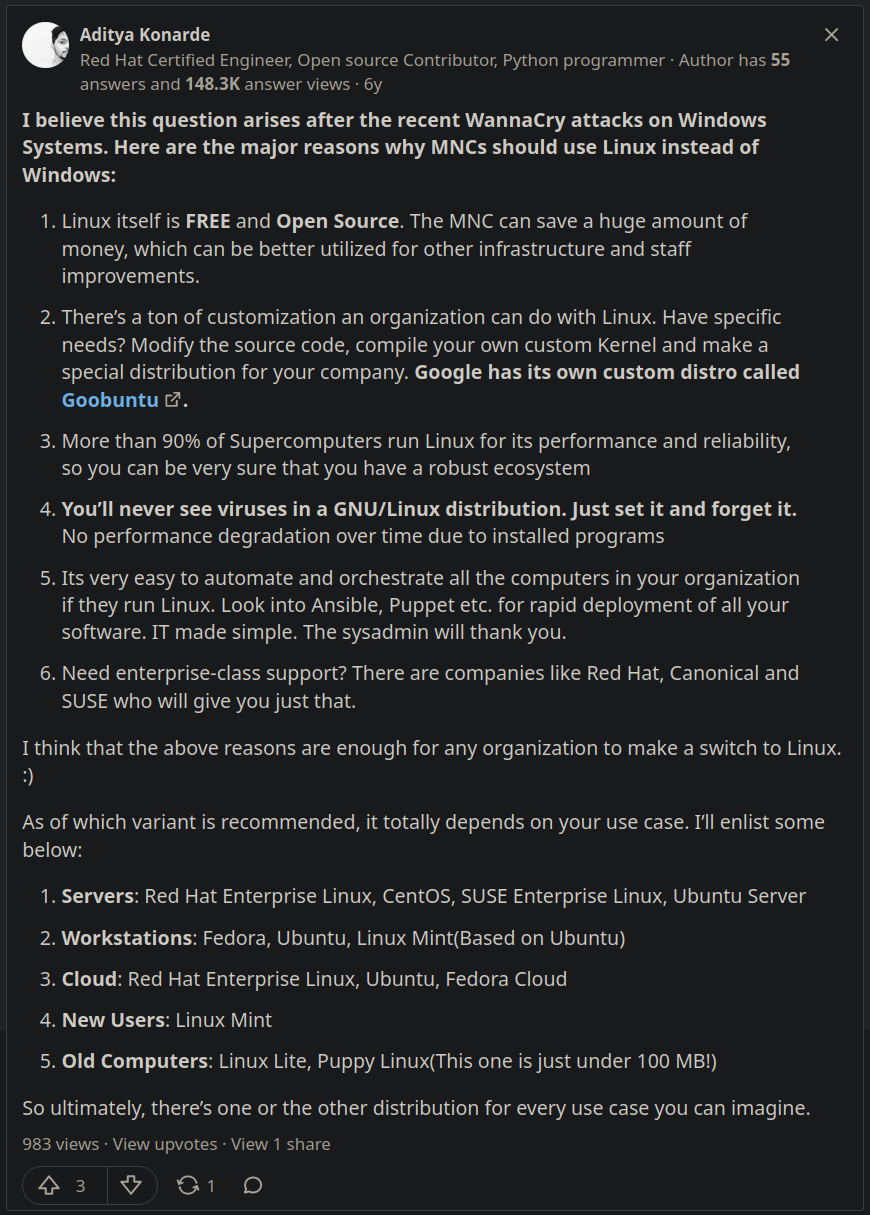
The text in the post's image literally says "just set it and forget it".
I think I get it now. You're using the word 'virus' as a synonym for an attack on computers. I'm using the word in the sense of a computer program that replicates on it's own and in practice also spreads and does some kind of damage. I get why we cannot agree. But the distinction has vastly different implications.
I read that quote in the context it was written in. And I'd partly agree. If you're talking with someone who has a small/moderately sized company and they're thinking about renewing their Sophos subscription. Hot-glue the USB-ports and protect their samba-share against being encrypted by some ransomware... You can't lump in highly targeted attacks on the top 5 companies in the world and every hypothetical scenario. Without any regards of statistical likelihood... If you want to condense it into a simple truth (which I think was the main point of that post), it's: There are no Linux viruses. And there probably won't be.
I think this is technically false. But practically true in the context it was written. And for most people anyways. If you want to talk about cybersecurity as a whole, your webserver and 150 PCs for your employers, I wouldn't recommend paying a 14 yo $50 to set it up Linux and fire and forget.
I agree. “just set it and forget it” is just bad, bad advice. I think I know where that comes from. I've seen >10 years old RHEL servers that hadn't been touched for quite some time. And a ridiculous hundreds and hundreds of days of uptime. They're kind of “just set it and forget it”... But... You gotta do it right. Do updates. Have it set up properly and with security in mind. Put in the effort. Lock it down. Don't expose them to the internet. Pay for longterm support and someone backporting patches and have them installed automatically etc.... You can't do it with any other OS (except for BSD and some specialized stuff). But you can't say “set it and forget it”. I agree. That's more than misleading. It's just false.